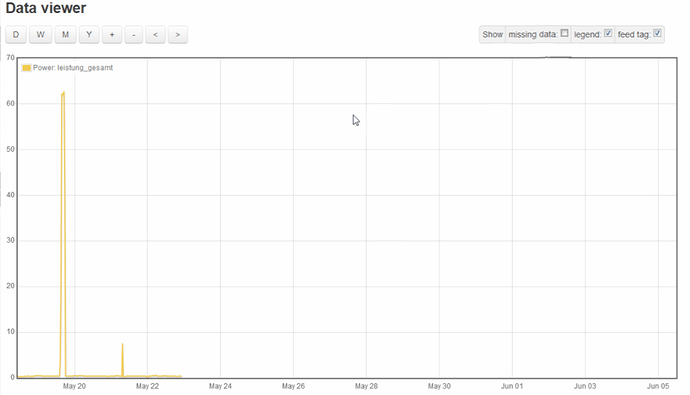
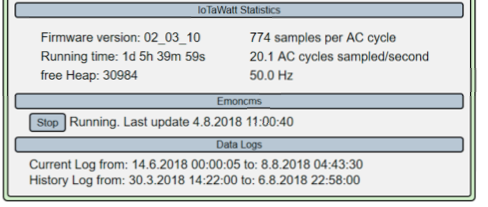
One of the best features of Iotawatt is the local storage of data on the SD card. Unfortunately, this feature could not save me in this case. Two iotawatts are located in the very north of Germany, they are connected to the same WLAN. Since the alpha version 02_03_06 strange things happen here with the time correction. The time jumps back and forth between 2018 and 2036:
5/21/18 06:47:11z EmonService: retry count 6350
5/21/18 06:47:21z EmonService: retry count 6360
5/21/18 06:47:31z EmonService: retry count 6370
2/07/36 06:28:17z timeSync: adjusting RTC by 559081614
5/21/18 11:01:24z timeSync: adjusting RTC by -559081615
5/24/18 06:03:01z timeSync: adjusting RTC by -2
2/07/36 06:28:16z timeSync: adjusting RTC by 558750417
5/25/18 07:01:20z timeSync: adjusting RTC by -558750417
5/26/18 21:01:18z timeSync: adjusting RTC by -2
2/07/36 06:28:16z timeSync: adjusting RTC by 558494812
5/28/18 06:01:24z timeSync: adjusting RTC by -558494812
5/29/18 14:55:14z timeSync: adjusting RTC by -2
5/31/18 21:01:28z timeSync: adjusting RTC by -2
6/03/18 14:02:03z timeSync: adjusting RTC by -2
Unfortunately, this means that the history log and the current log no longer function correctly. I assume it helps here only a reset of the two data logs?
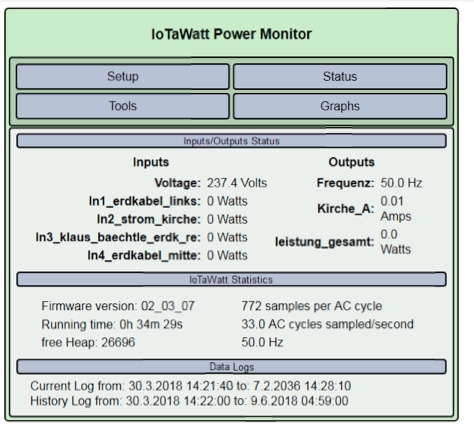
Here are the logs of both devices:
garage.txt (87.8 KB)
wohnung.txt (48.8 KB)